No really, Good old Games, is now doing movies. Â Of course they are somewhat gamer oriented, but I don’t see the infamous Super Mario Bros. movie..
Monthly Archives: August 2014
I don’t use Windows XP very often, but when I do…
(this is a guest post by Tenox)
I recently needed to install Windows XP. Because I don’t do that very often nowadays I decided to document the “pro way” of doing it.
First you should consider getting a volume license copy of Windows XP CD because it doesn’t require activation over the internet. The process below will work with any version, but it will require activation.
Then you need to download and install nLite which lets you add SATA/AHCI, network, display, audio, drivers and customize a fully unattended installation, including the product keys, and some tweaks like autologin, themes or show extensions/hidden files in explorer. Create your own bootable XP .iso file. You should probably test it in VMware/Vbox/Qemu first to see that all the settings are to your liking and the setup prompt screens are gone.
Second you need WSUS Offline Update, version 9.2.1 (which is the LAST version supporting Windows XP). It will let you roll out your own Service Pack 4 for Windows XP, including all the updates and goodies like .NET framework, Silverlight and DirectX updates. Create your own SP4 .iso file.
Booting Windows XP from a regular USB pen drive is notoriously difficult, so this is where ISOSTICK comes handy. Put both of the iso files on to the stick, insert to the PC and watch the magic happen.
It’s quite easy to integrate the SP4 in to the boot cd itself, but then it outgrows size of a physical CD, which is not a big deal with ISOSTICK, but I don’t mind installing the updates in a second step.
Finally if you need to install apps automatically you can consider something like Ninite.
Enjoy!
Netkeen
I’d never heard about this before, but a group reverse engineered Commander Keen, and re-built it as a network playable game!
Check it out at their site.
To build the source, you’ll need Borland C++ 5.0.2 and TASM 5.  Earlier versions may work but I haven’t tested.  The interesting thing with the networking is that they use the same code out of DOOM.
Fun with PGP 1.0
Well I got slightly bored, and thought I’d dig into some old crypto software. Â And PGP 1.0 was as good as any place to start.
Now one scandalous thing at the time was the inclusion of RSAREF 1.0, the RSA reference library which redistribution required a license that wasn’t exactly included with PGP.
A company called Public Key Partners (PKP) holds the exclusive
commercial license to sell and sub-license the RSA public key
cryptosystem. For licensing details on the RSA algorithm, you can
contact Robert Fougner at PKP, at 408/735-6779. The author of this
software implementation of the RSA algorithm is providing this
implementation for educational use only.
And wow was this fun at the time.  As far as I know this license lapsed on September 21, 2000.Â
And then there was this slight issue:
After Biham and Zimmermann go their food and sat down, Zimmermann took out a few pages of computer listings. Â Within minutes, Birham was finding fundamental flaws in Bass-O-Matic. Â Some of the flaws were subtle-weaknesses that made the algorithm susceptible to differential cryptanalysis, which was Birham’s speciality. Others were more embarrassing, like a conceptual error in Zimmermann’s algorithm that prevented the last bit of each byte from being properly encrypted. Â After ten minutes of Birham’s onslaught, Zimmermann realized that Bass-O-Matic was a lost cause.
So now you would be wondering, why would I even bother with what was a quickly abandoned encryption? Â Well I was bored, and I was more interested if I could locate the source to 1.0. Â What would be more interesting to me is to revive it onto somewhat more modern 32-bit platforms. Â Namely OS X, Win32 and MS-DOS.
With a little luck, I found the unix_pgp10.tar.gz, which does contain the source code for a Unix version of PGP! Â This version is more so geared to the SPARC of all things. Specifically it mentions:
Tested on SunOS 4.1 with gcc 1.39
However building on OS X was trival with changing the Makefile.  The CC had to be changed to reflect a 32bit build, and the DEFINES had to remove the HIGHFIRST define, as the x86 platform is little endian.
CC=cc -arch i386
DEFINES= -DUNIX -DPSEUDORANDOM -DUNIT16 -DPORTABLE
Is the relevant changes.
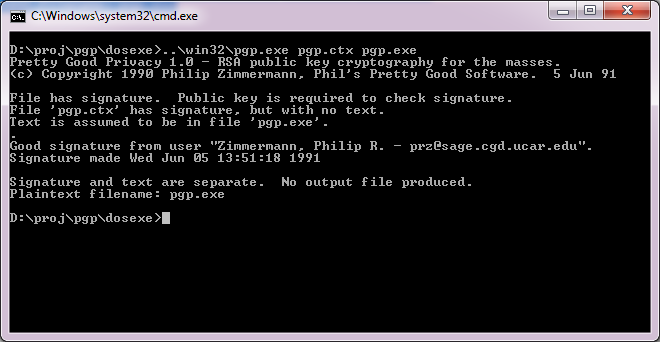
And even better it’ll work!
$ pgp pgp.ctx pgp.exe
Pretty Good Privacy 1.0 – RSA public key cryptography for the masses.
(c) Copyright 1990 Philip Zimmermann, Phil’s Pretty Good Software. 5 Jun 91
File has signature. Public key is required to check signature.
File ‘pgp.ctx’ has signature, but with no text.
Text is assumed to be in file ‘pgp.exe’.
.
Good signature from user “Zimmermann, Philip R. – [email protected]”.
Signature made Wed Jun 5 13:51:18 1991
Signature and text are separate. No output file produced.
Plaintext filename: pgp.exe
Wasn’t that great!
Now getting this to run on Windows was a little bit more of a challenge. Â I was going to build from the UNIX source code again, however both Visual C++, and Watcom C++ build an executable, but neither are able to add keys to the keyring, verify the executable reliably and deadlock all the time.
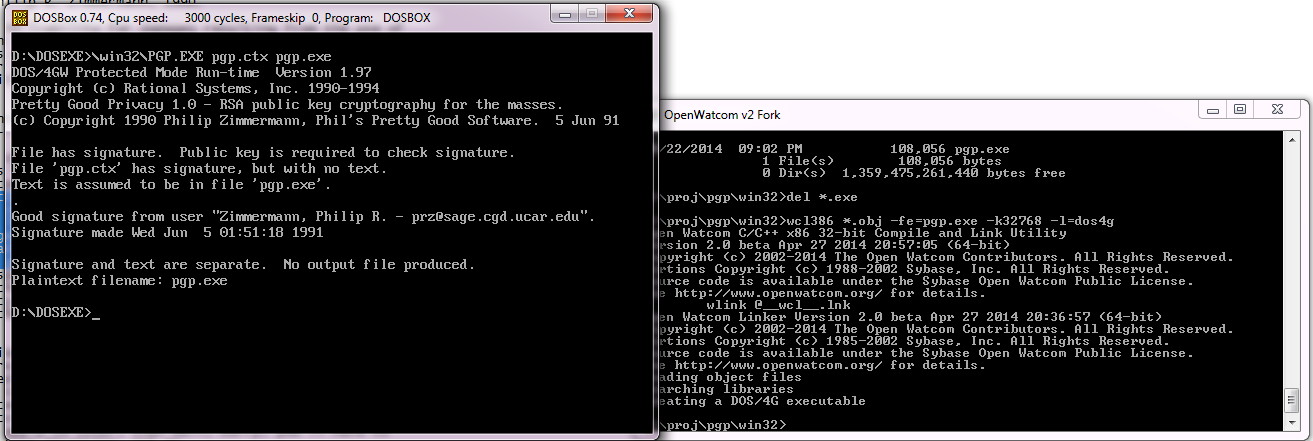
So I thought I’d get a little creative and start replacing some code from the MS-DOS version of PGP. It turns out that all I needed was rsaio.c & rsaio.h and I was able to build an executable. Â But I ran into other snags, and stack errors. Â A glance at the MS-DOS Makefile, and I saw that they had to up the stack size from the defaults. Â So I figured the same would hold true, and I picked a much larger 32kb stack for the heck of it. Â I mean it is 2014, and if you can’t handle a 32kb stack well..
Compiling on Visual C++ went like this:
cl386 -c /DPSEUDORANDOM /DUNIT16 /DPORTABLE *.c
cl *.obj /F32768 /Fepgp.exe
And for Watcom C++
wcl386 -c -dPSEUDORANDOM -dUNIT16 -dPORTABLE *.c
wcl386 *.obj -fe=pgp.exe -k32768
And now I can build for either compiler. Â And even better, it works!
Even for completness sakes, DOS4G/W works as well! Just remember to link for MS-DOS
wcl386 *.obj -fe=pgp.exe -k32768 -l=dos4g
And you should be good to go.
So what happened to PGP? Â Well version 2 used a more ‘acceptable’ encryption, the IDEA cypher, then the company was sold, IP was sold again and again. Â It’s still out there, mostly for email encryption.
While it sure did ignite the world on fire for a while, the overall difficulty of using it, combined with the ease of losing the private key and all your data is just too easy. Â But this really is the nature of the beast.
I guess you’ve all heard by now
that the internet broke pretty good yesterday. Â Apparently someone added some new routes, and it broke the 500,000 route limit in most BGP routers.
Oops.
But this has been a long time coming, even back in 2003 when I had a full BGP load I was running on a 7206vxr with 512MB of ram.
So if you had connectivity problems, that is what was going on.
Fun times for sure!