Sit down kids, it’s time for an old man rant.
So yeah, I have one of those clients who wants to use ‘one of those’ file sharing sites. UGH. Â I swear I’m to the point of just paying for an Office 365 subscription for them so I don’t have to deal with this kind of shit. Â So I hit the site on my phone, then it jumps to this genchatu.top site. Â Fantastic.
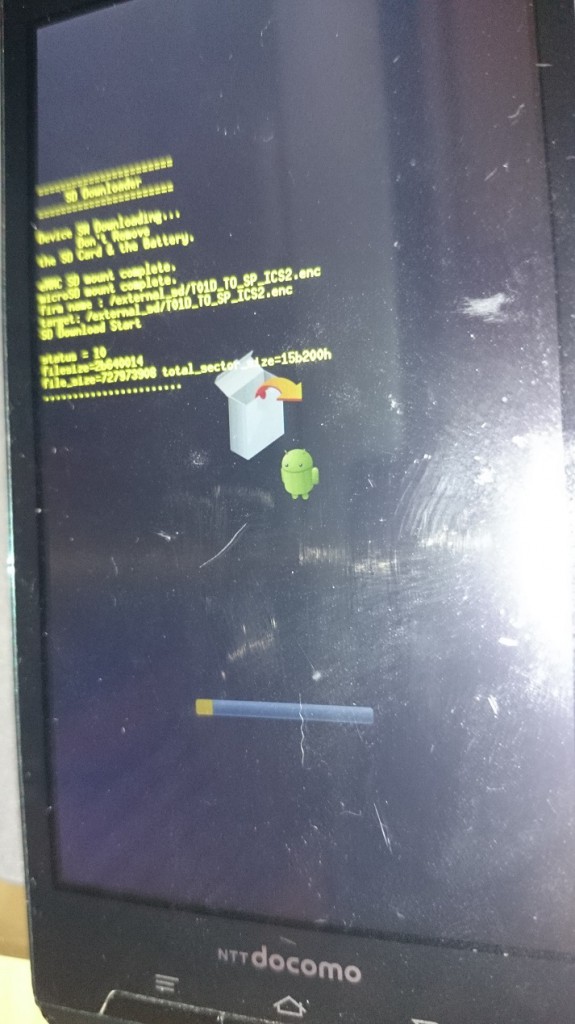
Then I’m alerted that my phone is 28.1% DAMAGED, and somehow my phone’s SIM card will be damaged! Â Yes, it’s one of these scam sites!
Oh no, my phone apparently may be already physically damaged? Â I guess this is once someone is tricked by this official Google looking image you’ll want to throw your phone against the wall. Â As any user of Android will tell you updates from Google are non existent, and anything that could infect your phone, well is pretty much your problem. Â You can beg the vendor, but lol, good luck.
I like to live dangerously, so yeah let’s look at the app.
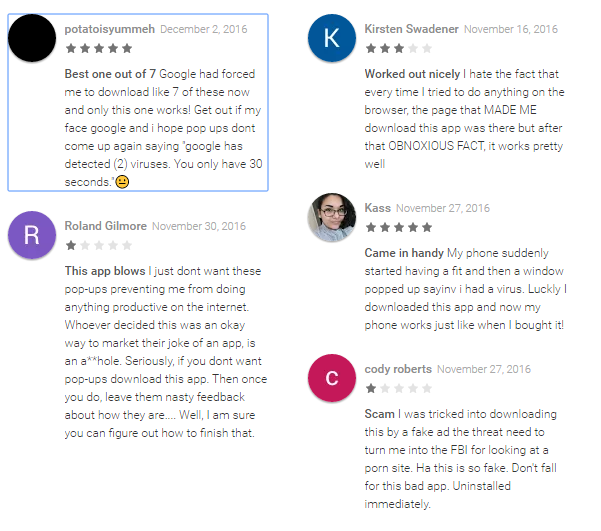
So with this scary and official looking thing it’s trying to railroad you into “Ace Cleaner” Â I don’t know how on earth they haven’t either been reported, or knocked out of the app store. Â I guess Google is busy teaming up with Facebook trying to figure out how to censor the new appropriately instead of trying to squash actual scam artists.
I honestly haven’t tracked any of these ‘reviews’ to see how many are just idiots, or how many are just ballot stuffers.
And of course you can’t just back away from the page, you get this nice thing along with something in java script that gets your phone to buzz and light up. Â Thanks Google! Â That’ll never get abused like the blink tag!
Oh no, I’ve been threatened to be blocked.
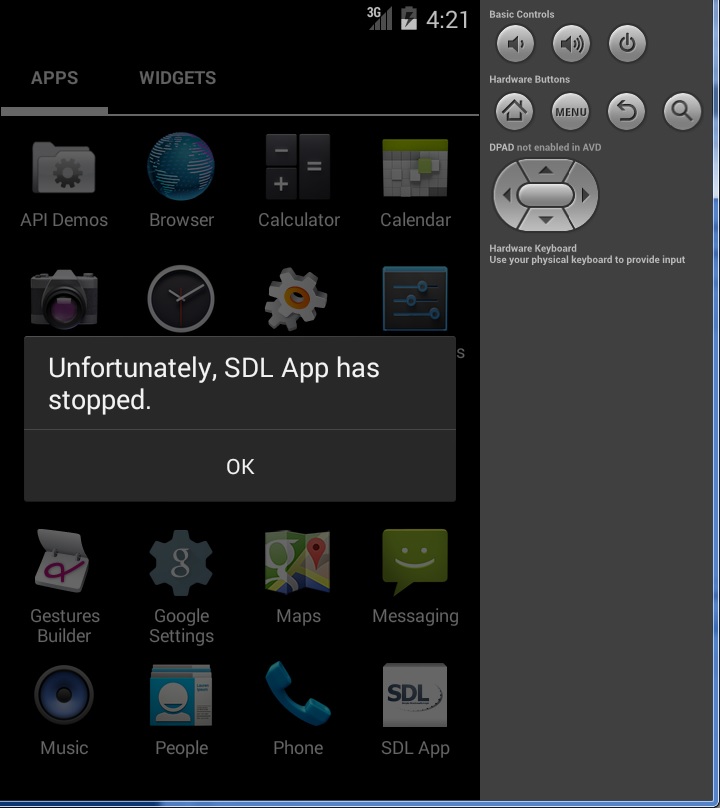
How bad can this crapware be?
Oh dear. Â From the application page, let’s take a look:
Where to go from here?
Seriously how do companies like this survive? Â I guess quite well. Â I guess I’m just more amazed by Google’s complacency in all of this. Â But at the same time they are an ADVERTISING COMPANY, and I’m the product, Android is just the TV programme to get me to watch their annoying ads. Â And considering their track record with illegal pharmacies, I guess it really is no surprise.
The truth is that no doubt that this kind of thing is just too profitable. Â And people will just fall time and time again for this trap.